Årsaken til at vi på dugnad oversatte og ga ut boken
«Hvordan knuse
overvåkningskapitalismen» av Cory Doctorow er at vi mener den tar
opp et viktig tema og bør leses av så mange som mulig. Temaene boken
tok opp, og det kommende valget, inspirerte nylig oss som sto bak
utgivelsen til å sende inn spørsmål til partiene sammen med et
eksemplar av boken. Vi er veldig spent på hva de ulike partiene
kommer til å svare. Spørsmålene er sendt til samtlige partier som er
representert på stortinget, men vi tar naturligvis imot svar også fra
andre partier. Det er for mange partier i Norge til å ta kostnaden
med å sende til alle, så vi begrenset oss til de som er representert
på Stortinget.
Her er brevet som ble postlagt til partiene tidligere i uka:
OM DIGITALE PLATTFORMER OG STORDATA – MED SEKS KONKRETE
FORSLAG
Det er en økende grad av mistillit til digitale plattformer fordi
den delen av vårt samfunn mangler helt grunnleggende demokratiske
kjøreregler. Begrepet «privatlivets fred» er i ferd med å dø som et
resultat av digitaliseringen. Som brukere har vi ikke kontroll over
våre personlige data og er helt frarøvet et digitalt privatliv. Dette
dels fordi samfunnet rundt oss samler inn data om oss og våre
bevegelser, samtidig som noen globale aktører samler data om
alle. Denne utviklingen er preget av kaos og manglende regulering.
Disse digitale utfordringene kan være vanskelig å formulere enkelt
inn i et partiprogram og enda vanskeligere å dekke helhetlig. Vi har
derfor valgt å sette søkelys på noen utvalgte områder som vi mener
partiene burde ta klare standpunkt til.
Personvern
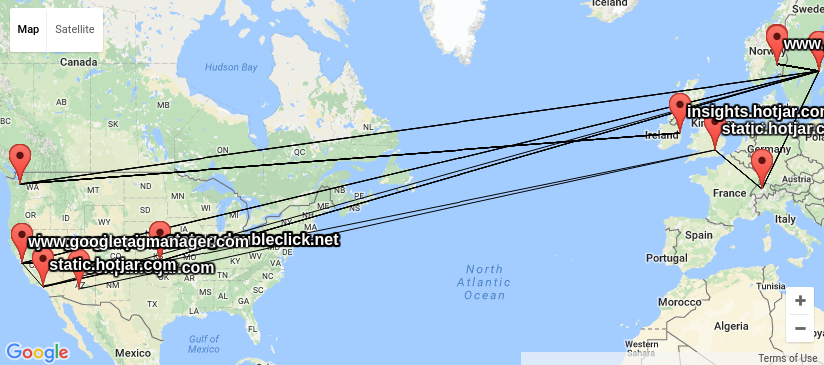
I følge tekologirådets direktør Tore Tennøe kan det, når offentlige
virksomheter som Sivilombudsmannen, Likestillings- og
diskrimineringsombudet og Medietilsynet alle deler brukerdata med
Google-tjenestene Analytics, remarketing audiences og annonsebørsen
Doubleclick, fort komme i veien for samfunnsoppdraget
deres. Uttalelsen kommer i forbindelse med en rapport fra
Teknologirådet som viser at en stor andel av offentlige virksomheter
deler personinformasjon om de som besøker virksomhetenes nettsider med
kommersielle
aktører.
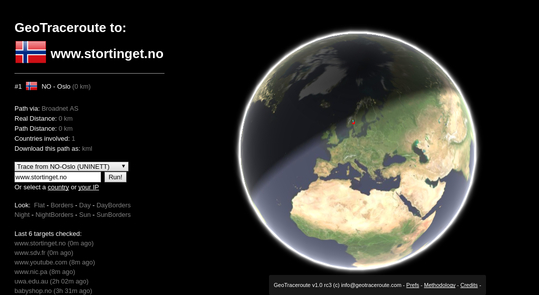
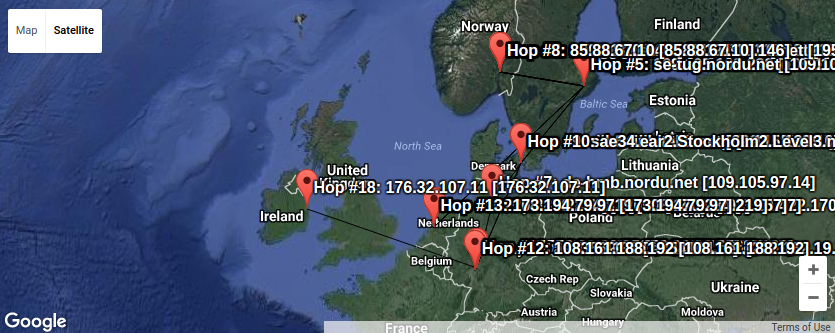
Stortinget er i følge rapporten en av disse.
I forbindelse med Covid 19 har bruken av videokonferanseløsninger
økt dramatisk. Løsninger som Microsoft Teams og Zoom har
åndsverksbruksvilkår som hindrer brukerne å undersøke sikkerheten i
systemene ved å forby omvent utvikling. Fri programvareløsninger som
Jitsi og Big Blue Button, har ikke slike begrensinger, kan tas i bruk
uavhengig av utenlandske leverandører og gir brukerne slik bedre
sikkerhet.
Facebook er ikke offentlig digital infrastruktur
Leder for det tyske datatilsynet BfDI, Ulrich Kelber, anbefalte sterkt
i et brev til tyske myndigheter nylig at de stengte sine
Facebook-sider og avslutter kobling mellom egne sider og Facebook.
Bakgrunnen er at bruken av Facebook ikke er i tråd med EU- og
EØS-lovgivingen om vern av privatsfæren, personvernforordningen
GDPR.
Massiv overvåkning av digitale brukere
De store globale plattformene samler inn data om oss alle gjennom sine
tjenester. Data akkumuleres og videreselges, med påstand om at
informasjonen er anonymisert. Data om geoposisjon er også noe
teleselskapene samler inn om alle brukere, selv de som har helt enkle
mobiltelefoner.
EUs personvernmyndighet, har i sitt arbeid med GDPR, presisert at
anonymisering ikke må forveksles med pseudoanonymisering, som fortsatt er
underlagt personvernlovgivningen, og at mobilers geografiske
plassering (lokasjonsdata) ikke kan anonymiseres.
En av mange saker som dokumenterer disse utfordringene er NRK som
kjøpte «anonymiserte» lokasjonsdata, og ved hjelp av enkel analyse kunne
identifisere enkeltindivider.
Grunnskolen i Norge har i stor grad tatt i bruk Internett-baserte
løsninger, og de fleste av disse samler inn personopplysninger om
elever og lærere som lagres på datamaskiner utenfor både Norge og
EU. I tillegg til å rapportere bruk til for eksempel Google
Analytics, så bruker mange av tjenestene datamaskiner eid av Amazon
og Microsoft. Dette fører totalt til en massiv spredning og innsamling
av personopplysninger utenfor skolene om elever i norske skoler.
Spørsmålene vi stiller til de politiske partiene er som følger:
- Er dere enige med det tyske datatilsynet om at offentlige
instanser ikke bør dele informasjon om sine ansatte og lesere med
selskaper i strid med GDPR, og derfor bør stenge sine
Facebook-sider?
- Er dere enig med Teknologirådet i at offentlig sektor bør velge
løsninger og verktøy som følger personvernprinsippene, og samler inn
minimalt med data til helt spesifikke formål?
- Bør det være mulig å bevege seg i Norge med mobiltelefon uten at
ens posisjon samles inn og selges videre av teleselskapene?
- Bør det offentlige velge videoløsninger som sikrer
brukernes rettigheter når det gjelder sikkerhet, personvern og
innsyn?
- Hva tenker deres parti man burde gjøre for å forhindre
massiv overvåkning av brukere i Norge?
- Er deling av elevenes personopplysninger til aktører utenfor
skolen, potensielt i strid med GDPR, en akseptabel kostnad for å
forenkle kommunenes drift av skoler?
Om det er behov for ytterligere avklaringer og
bakgrunnsinformasjon, ta gjerne kontakt! Epostadressen vår er til
Petter Reinholdtsen: pere-valg2021 (at) hungry.com. Spørsmålene samt
svarene vi mottar vil bli publisert.
Den internasjonale bakgrunnen
Internasjonalt pågår det en stadig bredere faglig og politisk
drøfting av de viktige bakenforliggende problemstillingene. Ett
eksempel er vedlagte bok der dr. Cory nettopp drøfter definerende
problemstillinger fom følger den nasjonale og internasjonale
utviklingen av «stordata». Boken peker også på helt konkrete
innsatsområder.
Når for eksempel Rand Worldwide viser til at Facebook
«radikaliseres», og når Facebook i sin tur sprer feilinformasjon om
coronaviruset med en forklaring om sine algoritmer, blir det
implisitte budskapet at maskinlæring og overvåkning kan endre vår
oppfattelse av hva som er sant. Begrepet «overvåkingskapitalisme» er
nå blitt det vanlig brukte ordet for å kjennetegne både beskivelsene
og debatten på dette vide stordata-området. Begrepet ble popularisert
i 2018-boken «Overvåkingskapitalismens tidsalder» av Shoshana Zuboff,
som igjen ledet Cory Doctorow til å skrive sin bok.
Legger ved boken fordi en gjennomgang er ment å være til hjelp
som nyttig bakgrunnsmateriale i det generelle politiske arbeidet på
dette stadig viktigere samfunnsområdet.
Boken ble oversatt til bokmål på dugnad og utgitt
samtidig med den engelske utgaven. Den kan fritt lastes ned
og også bestilles i trykt format på bokmål direkte fra trykkeriet. Nærmere
informasjon om utgivelsen fremgår av kolofon-siden.
Med vennlig hilsen
For Oversettergruppen
Petter Reinholdtsen (prosjektleder) og Ole-Erik Yrvin (gruppekontakt)
Hvordan knuse overvåkningskapitalismen (2021)
av Cory Doctorow, se også
https://craphound.com/category/destroy/
og
http://www.hungry.com/~pere/publisher/.
I dag er det en utbredt tro at maskinlæring og kommersiell
overvåkning kan gjøre selv en konspirasjonsteoretiker uten talegaver
til en magisk manipulator med evne til å finne de sårbare blant oss og
ved hjelp av argumenter skapt med kunstig intelligens, sette vettet
deres ut av spill og gjøre dem til flat-jord-tilhengere,
vaksineskeptikere eller til og med nynazister. Når RAND beskylder
Facebook for «radikalisering», og når Facebook i sin tur sprer
feilinformasjon om coronaviruset og bortforklarer det ved å henvise
til algoritmene sine, er det implisitte budskapet at maskinlæring og
overvåkning kan endre vår oppfattelse av hva som er sant.
Men hva om det finnes en annen forklaring? Hva om det er de
materielle forutsetningene som har endret seg til fordel for disse
manipulatorene? Hva om det er opplevelsen av å leve i en verden full
av ekte konspirasjoner, slik de viser seg i samhandlingen mellom rike
mennesker, lobbyistene deres og lovgiverne, der de enes om å begrave
ubehagelige sannheter og bevis på ugjerninger, slikt som gjerne kalles
korrupsjon — hva om det er denne opplevelsen som gjør folk sårbare for
de tåpelige konspirasjonsteoriene?
Som vanlig, hvis du bruker Bitcoin og ønsker å vise din støtte til
det jeg driver med, setter jeg pris på om du sender Bitcoin-donasjoner
til min adresse
15oWEoG9dUPovwmUL9KWAnYRtNJEkP1u1b.
Merk, betaling med bitcoin er ikke anonymt. :)